Your ORM superpower
Apache Cayenne™ is an open source Java object-to-relational mapping framework
Clicking on this link will load and send data from and to Google.
Key features
Modeler
Cayenne is distributed with CayenneModeler - a complete GUI mapping tool that supports reverse-engineering of RDBMS schemas, editing object-relational mapping projects, generating Java source code for persistent objects and other functions.
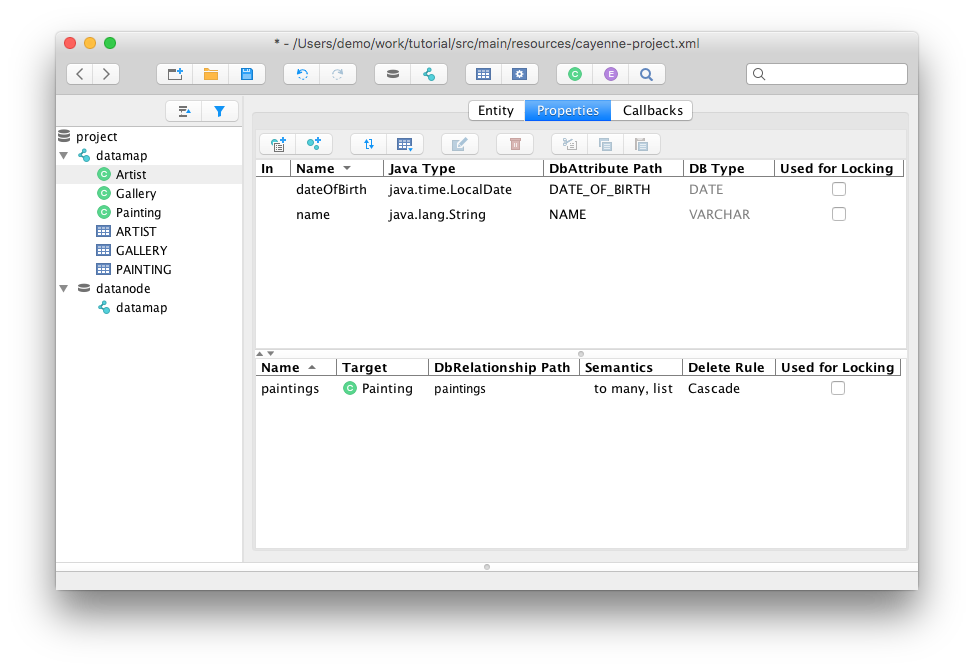
DB-first-flow
Cayenne allows you to design your data model in a single place - the database. Other layers (OR mapping and Java objects) are synchronized automatically via CayenneModeler or a build script, so you don't have to repeat yourself. Such an approach is called "database-first". It saves you development time and prevents errors by ensuring that your model is in sync across multiple layers. It is also quite flexible. It works well with common DB migration frameworks like Liquibase or Flyway, allows object structure customizations and is designed for iterative schema evolution.
Transparent transactions
Most ORM frameworks require you to manage transactions manually or with external tools like Spring. Also you must always ensure you stay within transaction bounds when traversing relationships between objects. Cayenne takes a notably different approach, freeing you from writing lots of trivial code. Transaction management happens automatically behind the scenes. Object graphs can be expanded lazily on demand, without any special considerations.
At the same time Cayenne works well with external transaction managers. It also has its own transaction API that can be used to run multiple operations atomically in regards to DB commit/rollback. The good thing is that it is completely optional and should be used only when needed.
Object Context
At the heart of Cayenne's persistence API lies ObjectContext. ObjectContext can be thought of as a unit of work. It has its own copy of persistent objects. While vaguely similar to JPA EntityManager, ObjectContext is closer to a version control client. It is not connected to the database except when a read or write operation is in progress, it doesn't hold on to any resources (such as DB connections), and doesn't need to be closed.
As a result ObjectContexts are serializable and rather lightweight. Contexts can be nested (a child context can read/write from/to its parent without affecting the DB). There is even a version of ObjectContext that can run in an entirely different JVM from the main app, and communicate with the app via a binary web service.
Extension API
Cayenne stack is built around a small dependency injection (DI) container responsible for configuring and binding all framework services. It provides a simple API to define custom implementations of core services and strategies or add extensions to the existing ones (e.g. custom value types). Additionally, many things can be configured via system properties.
Cayenne is truly modular. The above-mentioned DI container supports autoloading of extra modules from the classpath. Cayenne itself takes advantage of this, isolating various optional features and integrations into optional modules. You can do the same with your own code.
Generic Objects
Traditional Java ORMs depend on bytecode generation or dynamic proxies to "connect" persistent objects with the framework. In constrast, Cayenne objects implement a simple API contract to interact with the ORM runtime, but otherwise can be structured arbitrarily, not requiring any annotation or "enhancement".
This opens up some interesting possibilities. E.g. Cayenne provides a Map-based "generic" persistent object that can be dynamically mapped to any entity. This means that an ORM model can be created in runtime without recompiling the code. Combined with the DB reverse-engineering feature, this allows building completely generic data tools and services.
Data Encryption
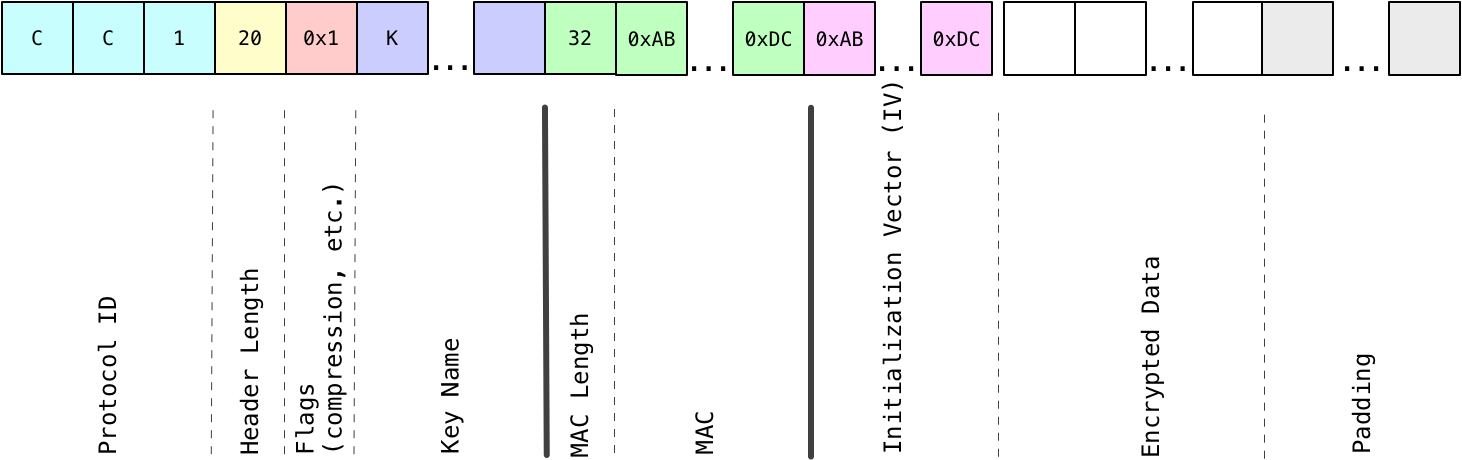
Traditionally, protecting DB data at rest stops at encrypting entire hard drive partitions. Cayenne goes a few steps further, offering a more secure and flexible solution - the "cayenne-crypto" module with field-level data encryption.
You can designate any number of columns in multiple tables in your model as encrypted, and Cayenne will transparently encrypt and decrypt data with minimal overhead. The default encryption algorithm is AES/CBC/PKCS#5 with a 128 or 256-bit key. Other useful features are key revocation, data compression, and HMAC signatures.